Imagine a database that has hundreds or even thousands of people with their name, age, address, phone number, email address, and countless other details about them. Now imagine there is also an email account that people have sent their deepest and darkest struggles: porn addiction, coping with past abuse, betrayals in marriage...
Now imagine that criminals gain access to that information! 🥷
How would you feel if that were your information leaked? How would the local community respond? If it were a church, would it be a laughing stock? Would people want to attend a church that had a data breach? Would a congregation call for resignations? 😱
In all honesty, it would give me a lot of pause if I were invited or attended. 🤨
This is the reality for churches, denominations, and missions organizations. They keep a lot of sensitive data, but most have not taken any concrete steps toward protecting that data. Worse, they often keep church member data in personal data services like a personal Dropbox account. 🤦 That's incredibly risky for a church today, who wants to go to a church that acts cavalier with their personal information? Who wants a shepherd who doesn't guard the sheep? 🐑
So here's the big question: how does a church, especially the average church that doesn't necessarily have a lot of budget or expertise, reduce the risk of having the information of their visitors and members stolen?
The answer lies in utilizing a framework, specifically, the Center for Internet Security Controls Version 8 Implementation Group 1 (CIS v8 IG1). Now, in certain countries or even states, you will also need to implement additional frameworks (GDPR, PDPA, etc.), but these usually match up quite closely with CIS v8 IG1. Likewise, insurance companies may publish requirements or determine premiums based on security practices, but they will usually align closely with CIS controls. CIS v8 IG1 is the foundation to build on top of! 🏗️
CIS controls are very straightforward and reduce risk by upwards of 90%. 😎 For example, control 5.2: "Use unique passwords"... "at a minimum, an 8-character password for accounting using MFA..." A church would then setup their Microsoft 365 Business Premium donation to require 8-characters and use either Azure Active Directory Conditional Access or Azure Active Directory Security Defaults to enforce multifactor authentication (MFA).
You can download the CIS controls from their website:
https://learn.cisecurity.org/cis-controls-download
We implement CIS IG1 (and IG2 elements) for our church and missions clients. When I'm doing implementation or an audit, I like to use the CIS provided Excel sheet and color code items based on completion: green = done, yellow = partial compliance, red = not compliant. I'll often mark off additional items as well because it helps visualize the security posture of the church beyond IG1. 💪
Here's what control 6 might look like if you were using all the features of the Microsoft 365 Business Premium donations but still had a traditional password based VPN and a legacy application that didn't support MFA:
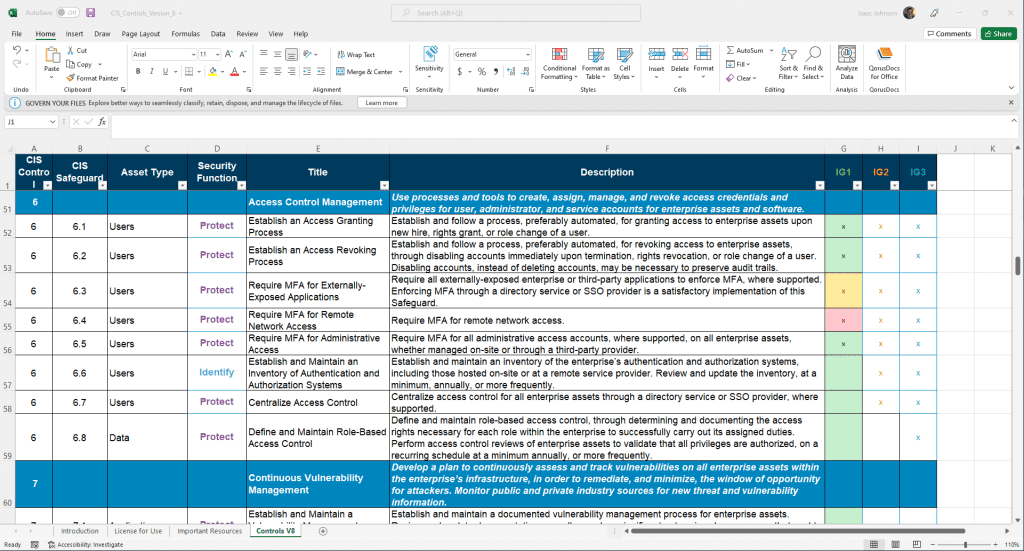
Start working on moving your church into the green and you'll dramatically reduce the risk to your members, your reputation, and your liability to lawsuits.



